Experts call for rigorous audit to protect California recall
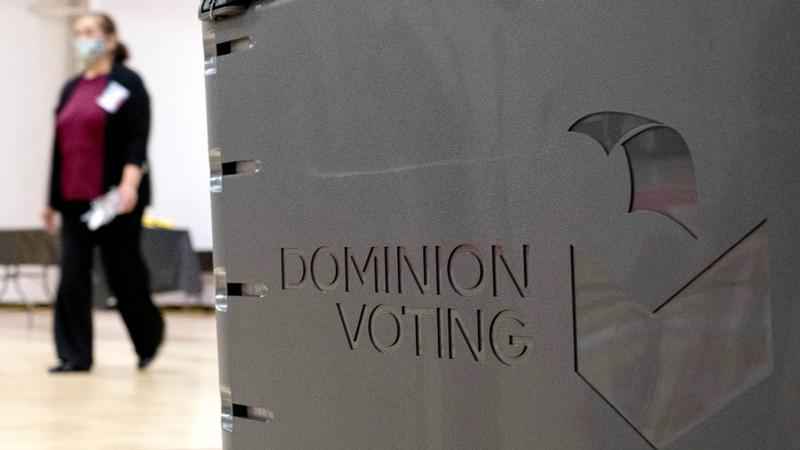
FILE - In this Jan. 4, 2021, file photo a worker passes a Dominion Voting ballot scanner while setting up a polling location at an elementary school in Gwinnett County, Ga., outside of Atlanta. A group of election security experts will ask California officials, Thursday, Sept. 2, to take additional steps to protect the upcoming governor’s recall election after the unauthorized release of voting system software in other states.[AP Photo/Ben Gray, File]
A group of election security experts on Thursday called for a rigorous audit of the upcoming recall election for California’s governor after copies of systems used to run elections across the country were released publicly.
Their letter sent to the secretary of state’s office urges the state to conduct a type of post-election audit that can help detect malicious attempts to interfere.
The statewide recall targeting Democratic Gov. Gavin Newsom, set for Sept. 14, is the first election since copies of Dominion Voting Systems’ election management system were distributed last month at an event organized by MyPillow CEO Mike Lindell, an ally of former President Donald Trump who has made unsubstantiated claims about last year’s election. Election offices across 30 states use the Dominion system, including 40 counties in California.
Election security experts have said the breaches, from a county in Colorado and another in Michigan, pose a heightened risk to elections because the system is used for a number of administrative functions — from designing ballots and configuring voting machines to tallying results. In the letter, the experts said they do not have evidence that anyone plans to attempt a hack of the systems used in California and are not casting blame on Dominion.
“However, it is critical to recognize that the release of the Dominion software into the wild has increased the risk to the security of California elections to the point that emergency action is warranted," the experts wrote in their letter, which was shared with The Associated Press.
The eight experts signing the letter include computer scientists, election technology experts and cybersecurity researchers.
Jenna Dresner, a spokeswoman for Secretary of State Shirley Weber, said the 40 counties in California using Dominion employ a different version of the election management system that meets various state-specific requirements. She outlined numerous security measures in place to protect voting systems across the state. That includes regular testing for vulnerabilities, strict controls on who has access, physical security rules and pre-election testing to ensure that no part of the system has been modified.
“California has the strictest and most comprehensive voting system testing, use, and requirements in the country, and it was designed to withstand potential threats,” Dresner said in a statement to the AP.
The security experts want California counties using Dominion’s election management system to do what’s known as a “risk-limiting audit,” which essentially uses a statistical approach to ensure that the reported results match the actual votes cast. California also uses paper ballots, which makes it easier to verify results.
The letter said differences between the leaked Dominion software images and the versions used in California are relatively minor. The experts said thousands of people now have access to the underpinnings of Dominion’s election management system, including some who may have access to voting equipment.
“That increases the risk of undetected outcome-changing cyber-attacks on California counties that use Dominion equipment and the risk of accusations of fraud and election manipulation which, without rigorous post-election auditing, would be impossible to disprove,” the letter states.
A majority of voters are expected to cast mail ballots during the recall, returning them through the U.S. Postal Service or by drop boxes in their counties.
California law already requires counties to hand-count ballots from a random sample of 1% of the precincts after an election. Although the state has conducted a pilot program with risk-limiting audits, Dresner said state law does not currently allow one for the recall election. It’s not clear whether that could be changed with less than two weeks to go before the election.
Among those signing the letter was Harri Hursti, a voting technology expert who was at the Lindell event in South Dakota. Hursti said he received three copies of the Dominion election management system — one an image of the system used in Antrim County, Michigan, and the other two from Mesa County, Colorado. In a sworn declaration filed in federal court in Georgia, Hursti said the copies were later made available for online download.
He said the release gives hackers a “practice environment” to seek vulnerabilities in the system and a road map to avoid defenses. All hackers would need is physical access to the systems because they aren’t supposed to be connected to the internet.
Philip B. Stark, a professor of statistics at the University of California, Berkeley, who also signed the letter, likened it to the difference between a bank robber having a blueprint of a vault and having an exact replica of the vault to practice attacks.
“That’s what this is,” he said. “They basically have an exact copy of the thing they’re trying to break into.”
Experts say attacks could create technical problems that can cause machines to malfunction, manipulate ballot design or even target results.
A Dominion representative said the company was aware of reports about the unauthorized release of the system images and had reported it to authorities. The company said federal cybersecurity officials don’t view the breach as significantly increasing the risk to elections.
But Stark said the sheer number of people who now have access to the information makes this breach especially serious. While it’s possible the information already was in the hands of the Russians or other adversaries, there had been considerable expense and legwork involved in getting it, he said. Now that’s not the case.
“What this has done on some level is democratized access to the information that would be needed to make a cyberattack on Dominion systems,” Stark said.
Compounding the threat is a finding by voting technology specialist J. Alex Halderman that even a voter has enough physical access to implant malware, Stark said.
“So if you have someone who can do the technical work of devising a cyberattack, then it could actually be deployed by a voter, by an insider, by a vendor, by whoever,” he said. “It’s just really multiplied the number of people who are in a position to do harm to our elections by a very large factor.”
Halderman, director of the University of Michigan’s Center for Computer Security and Society, made those observations after examining Dominion voting equipment used in Georgia as an expert witness in a long-running lawsuit challenging the use of those machines.
The release of the system images follows an effort by Republicans to examine voting equipment that began soon after the November election as Trump challenged the results and blamed his loss on widespread fraud, even though there has been no evidence of it.